2023 CULytics Summit
2023 CULytics Summit
Microsoft Conference Center, Redmond, WA
Aunalytics to attend and speak at the 2023 CULytics Summit in Redmond, WA
Aunalytics is thrilled to attend and speak at the 2023 CULytics Summit—in-person for the first time after a three year hiatus! Aunalytics is excited to participate in two speaking sessions. Ryan Wilson, VP, Client Relationships, will be presenting a demo of the Daybreak™ for Financial Services solution which enables credit unions to more effectively identify and deliver new services and solutions so they can better compete with large national banks. Meanwhile, Taylor Oake, Account Executive – Enterprise Analytics, will be joining Brent Hepner of 3Rivers FCU to present the case study, “Discovering Business Value Through AI-Powered Business Intelligence & Predictive Analytics: A Successful Partnership.”

Ohio Credit Union League InVest48
Ohio Credit Union League InVest48
Hilton Downtown Columbus Tower, Columbus, OH
Aunalytics to attend InVest48, the Ohio Credit Union League's Annual Conference
Aunalytics is pleased to attend InVest48, the annual conference of the Ohio Credit Union League. Aunalytics will be meeting with attendees and giving demos at booth #416. Representatives from Aunalytics will be educating attendees on how financial institutions can use AI-driven insights to improve customer and member engagement and increase wallet share. Event attendees can also learn more about the Daybreak™ for Financial Services solution which enables credit unions to more effectively identify and deliver new services and solutions so they can better compete with large national banks.

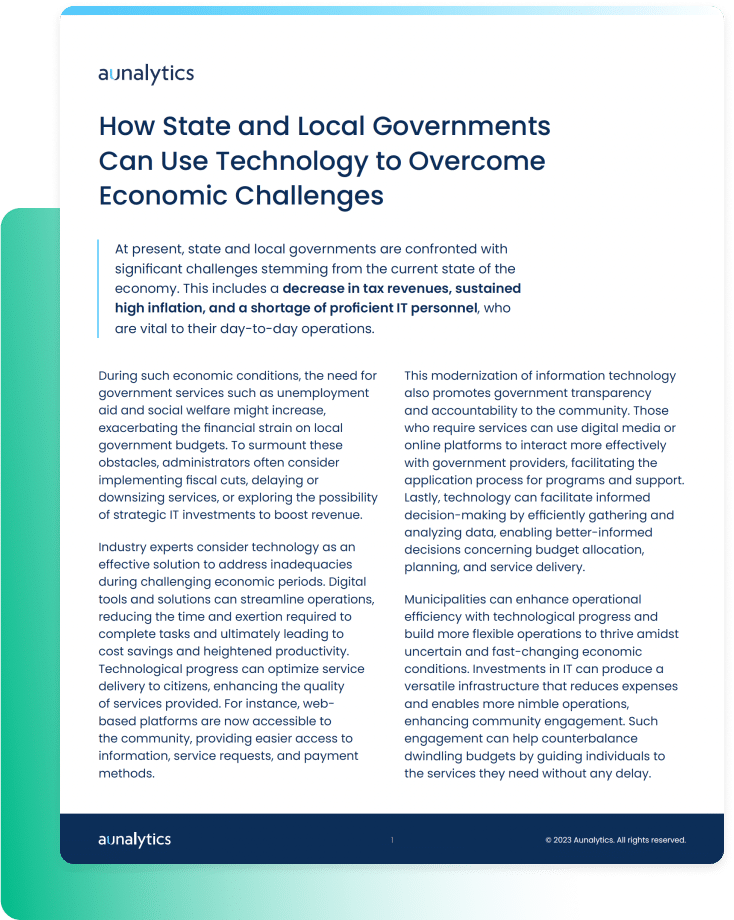
How State and Local Governments Can Use Technology to Overcome Economic Challenges
How State and Local Governments Can Use Technology to Overcome Economic Challenges
At present, state and local governments are confronted with significant challenges stemming from the current state of the economy. This includes a decrease in tax revenues, sustained high inflation, and a shortage of proficient IT personnel, who are vital to their day-to-day operations. Industry experts consider technology as an effective solution to address inadequacies during challenging economic periods.
Fill out the form below to receive a link to the article.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
Government Resources
Nothing found.
How State and Local Governments Can Use Technology to Overcome Economic Challenges
How State and Local Governments Can Use Technology to Overcome Economic Challenges
At present, state and local governments are confronted with significant challenges stemming from the current state of the economy. This includes a decrease in tax revenues, sustained high inflation, and a shortage of proficient IT personnel, who are vital to their day-to-day operations. Industry experts consider technology as an effective solution to address inadequacies during challenging economic periods.
Related Content
Nothing found.
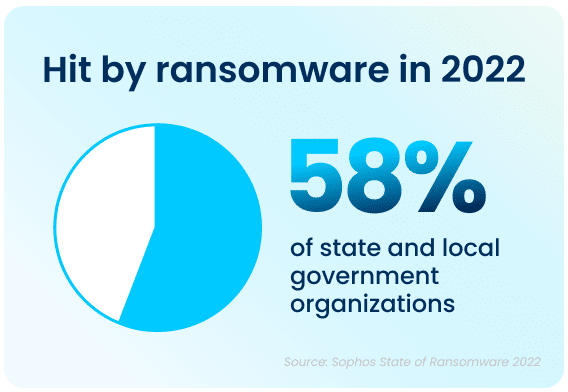
Local and State Government Cyberattacks Prove that Security is a Necessity
Cyberattacks are a constant threat to organizations of all sizes. State and local governments are no different, having experienced significantly more cyberattacks than they did in previous years, and are at very high risk of bad actors slipping into their networks. To gain a better understanding of the current attack environment and track changes over time in ransomware trends, Aunalytics security partner Sophos commissioned an independent, vendor-agnostic survey of 5,600 IT professionals across multiple industries in mid-sized organizations across 31 countries. While it’s true cyber insurance has been playing a greater role in helping organizations improve their ability to recover from attacks, survey responses clearly indicate that ransomware poses a rising threat to government organizations.
Government Cyberattacks Increase From Previous Years
Ransomware attacks have increased significantly over the past year—58% of state and local government organizations surveyed were hit by an attack in 2021, up 70% from 2020. Bad actors are now considerably more capable of attacking organizations and executing harmful tactics at scale. The Ransomware-as-a-Service (RaaS) model is one cause of last year’s increased attacks, as the required skill level for bad actors to hamper the day-to-day operations of an organization has gone down significantly.
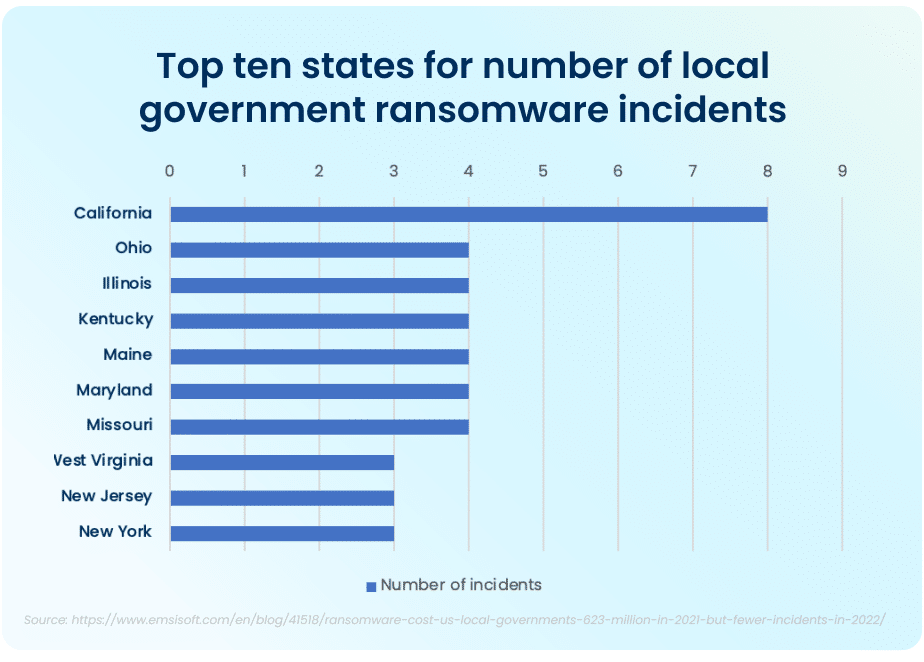
The top ten states that had to deal with the maximum amount of total ransomware attacks in the public sector in 2021 were California, who experienced the most attacks total, Ohio, Illinois, Kentucky, Maine, Maryland, and Missouri. While California took the lion’s share of attacks, with 8 major ransomware incidents, the other six states had four major incidents each.
FBI Cyber Division Survey Lists Examples of Ransomware Attacks
The Federal Bureau of Investigation (FBI) Cyber Division lists examples of several ransomware attacks that impacted state and local government organizations in their 2022 Private Industry Notification. This list contains evidence showing the impact these attacks can have on local communities.
For example, in January 2022, following a ransomware attack, a US county had to take all their systems offline and close all public locations in order to run an emergency response plan and restore all their data from backups. This action disabled all the cameras in the local county jail and deactivated automatic doors, resulting in severe safety concerns and a complete lockdown of the facility. A different county had their data—with residential and personal data—held ransom in an attack. When the ransom was not paid, all of the data was posted on the Dark Web in retaliation.
Rising Complexity of Ransomware Attacks
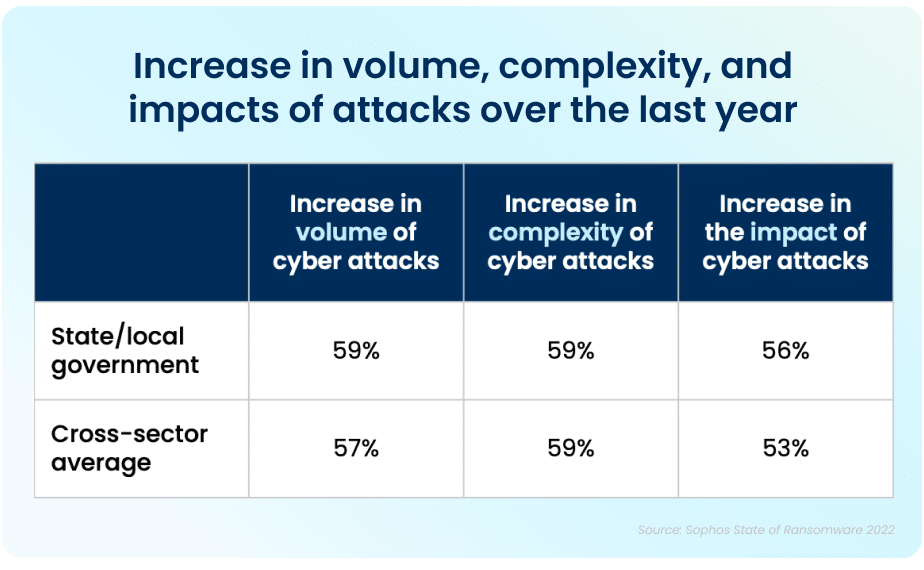
Apart from the rising prevalence of these attacks, the sheer complexity of each attack is also on an upwards trajectory. While the manufacturing and production industry reported the lowest rate of ransomware attacks, over half of all respondents reported their organization was injured by bad actors. The reality is that every organization is at high risk of cyberattack. In 2021, 59% percent of government organizations who experienced cyberattacks saw the complexity of the attacks increase, while a similar 59% saw an increase in the overall volume of cyberattacks.
Data Recovery Rates Are Improving
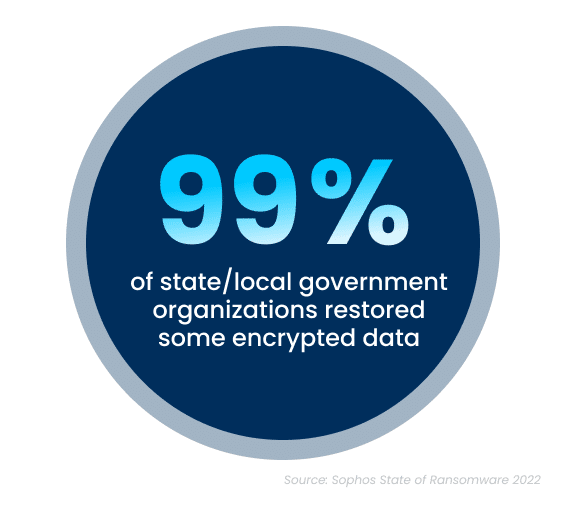
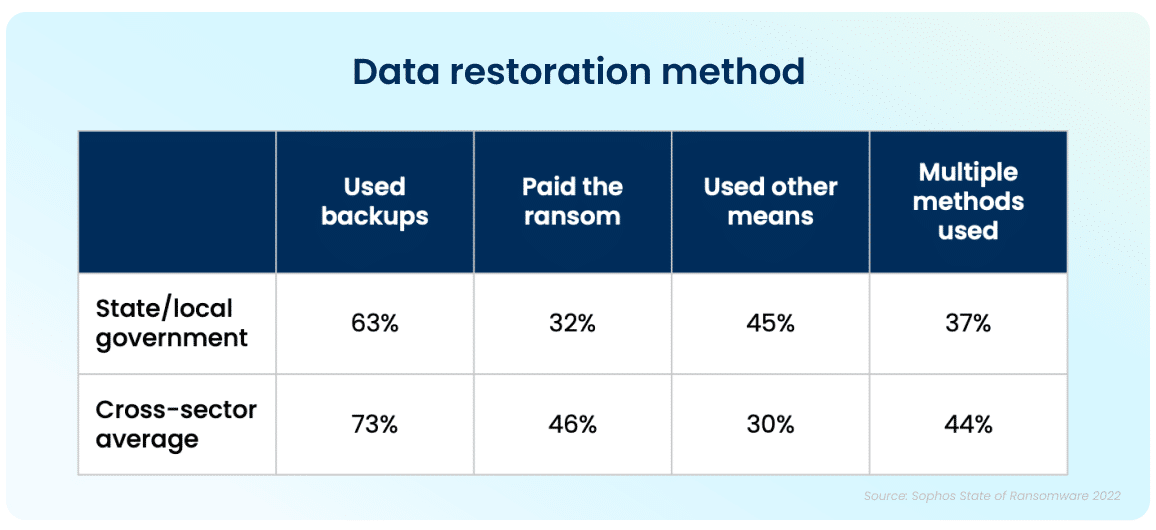
While the increase in cyberattacks paints a bleak picture, there is a silver lining to this dark cloud. Ninety-nine percent of government organizations were able to get at least some of their encrypted data back. The top method used to restore data was performed via existing backups, which were used by 63% of organizations whose data was encrypted in an attack. Unfortunately, despite the utilization of backups, 32% of the affected organizations still had to pay a ransom to ensure that more of their data was restored.
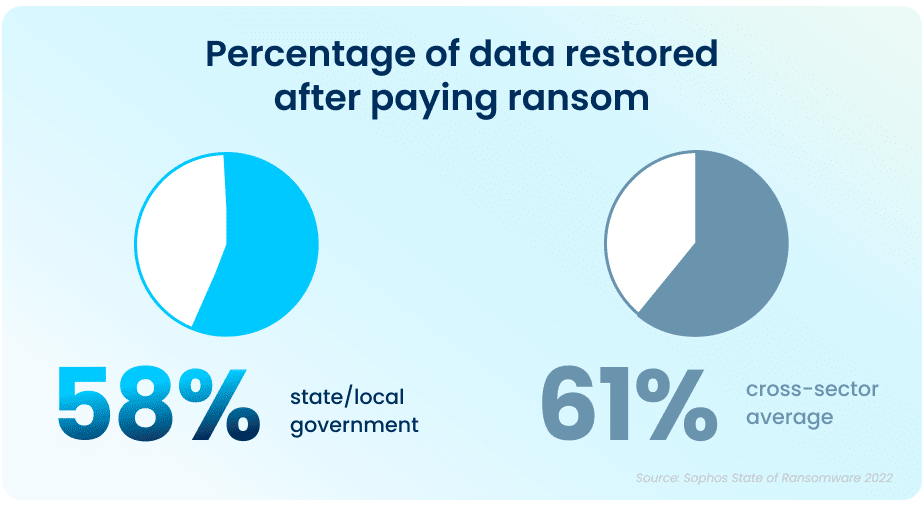
While paying a ransom typically allows organizations to get some data back, it is proving to be less effective than in years past. On average, in 2021, organizations that paid a ransom only got back 58% of their data, a considerable drop from 70% in 2020.
In April and June 2022, respectively, the states of North Carolina and Florida were the first states to prohibit state and local government organizations from paying ransoms to any bad actors. Arizona, Pennsylvania, Texas and New York are considering similar legislation. While the exact impact of this cannot be determined yet, this is expected to dissuade ransomware attacks on all organizations.
This highlights the importance of employing multiple methods to restore data—utilizing backups in particular can improve the speed of recovery and increase the amount of data that can be recovered in the event of an attack.
But It Doesn’t End There
The Sophos State of Ransomware In State and Local Government 2022 survey has revealed that ransomware continues to be an imminent threat for state and local government organizations. For many, choosing to work with an experienced partner with expertise in cybersecurity not only improves your chances of getting approved for the right amount of cyber insurance coverage, but can also ensure that companies see a higher return on investment, and improved ability to both prevent and mitigate attacks in the future. Aunalytics provides Disaster Recovery Services, which is further coupled with a comprehensive backup and archival strategy. This allows state and local government organizations like yours to remain confident so that you are prepared should you encounter a disaster event. We partner with industry leaders to replicate your critical infrastructure so you are prepared for anything.
2023 Fintech Meetup
Fintech Meetup 2023
Aria, Las Vegas, NV
Aunalytics to attend the 2023 Fintech Meetup in Las Vegas as Bronze Sponsor
Aunalytics is excited to attend the 2023 Fintech Meetup in Las Vegas, Nevada. Aunalytics will be meeting with attendees and giving demos at booth SC1 on how financial institutions can use AI-driven insights to improve customer and member engagement and increase wallet share. Event attendees can learn more about the Daybreak™ for Financial Services solution which enables community banks and credit unions to more effectively identify and deliver new services and solutions so they can better compete with large national banks.
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
While advancing technology offers significant benefits, it has also made it easier for those who seek to gain an advantage by exploiting others. An attack can be devastating for any business and impact it for many years to come—today’s organizations need to move toward security maturity by utilizing multiple lines of defense against cybercrime.
Fill out the form below to receive a link to the article.
Aunalytics is a data platform company. We deliver insights as a service to answer your most important IT and business questions.
Related Content
Nothing found.
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
Security Maturity Improvement is Imperative as Cyberattack Risks Remain High
While advancing technology offers significant benefits, it has also made it easier for those who seek to gain an advantage by exploiting others. An attack can be devastating for any business and impact it for many years to come—today’s organizations need to move toward security maturity by utilizing multiple lines of defense against cybercrime.
Related Content
Nothing found.
When Was the Last Time You Checked on Your Internet Security?
Internet security—a combination of security measures put into place to protect any transaction or activity made over the internet—is one of the most necessary forms of security your business could possibly have.
Everything we do, every day, is virtually always online—even though we sit next to Deborah, we usually send her files through a document sharing program like SharePoint or Google Docs. We don’t walk over with a paper file and hand it to her often, if ever. When thinking of our daily interactions with the internet in corporate environments, it becomes more and more startling that many of us are not aware what our role in our company’s corporate security actually is. Some think it’s remembering to change your password, while others know there are specific steps you can take to better secure your network from the malicious creepy crawlies.
They're Everywhere
Security threats are as widely varied as the content on the internet and can include everything from the well-known malware and phishing to Wi-Fi threats, computer worms, and botnets.
How many people do you know that take their work devices with them to coffee shops for a change of pace? As safe and normal as this may seem, there are multiple kinds of Wi-Fi threats that can piggyback onto public Wi-Fi and open networks. The three most common types of Wi-Fi threats are Man-in-the-Middle (MitM), Rogue Networks, and Packet Sniffing.

Let’s break this down a little bit:
- Man-in-the-Middle (MitM) attacks are generally the most common type of Wi-Fi threat. In its most basic form, a MitM attack is when a bad actor is able to intercept and read messages between users who believe they are only speaking to each other privately, essentially eavesdropping on their conversation and any confidential information that is being shared.
- Rogue Networks are fake Wi-Fi networks that attackers set up to confuse users into giving hackers access to their devices. Rogue networks can easily masquerade as trusted networks, especially those at locations like your favorite bookstore or coffee shop. If you see a guest network, only use it if the network is secured and you need a password to log into the network. This can help ensure your computer and other tech is better protected and is less likely to end up on a rogue network.
- Packet Sniffing, sometimes known as Packet Analyzers, can monitor traffic on a network. This malicious attack can intercept data while it is being transmitted across your network and provide hackers with details on the data package’s contents. Using this method, bad actors can also introduce errors that can corrupt your system.
Wi-Fi threats aren’t the only internet threats to your corporate security. Botnets, a network of private computers that are infected with malicious software and often controlled by a single user, are most often used for denial-of-service (DoS) attacks, and sending out spam messages for users in your network. Similarly, a computer worm, a software that can copy itself multiple times, can spread across your network quickly, leaving mass destruction in its wake.
What Now?
With the threat of bad actors finding a hole in your network at any point in time, it’s impossible to ignore your cyber security. Risks are becoming higher as viruses and malware become increasingly complex, setting companies up for difficulties when navigating the process of recovering data, and further difficulties of finding easily obtainable cyber security insurance following a security event. Finding and utilizing a trusted partner can help you keep your network safe and consistently monitored with services like a 24/7/365 monitored Security Operations Center (SOC), help attaining industry security compliance requirements, and developing a Backup and Disaster Recovery (DR) plan for when the unexpected strikes.